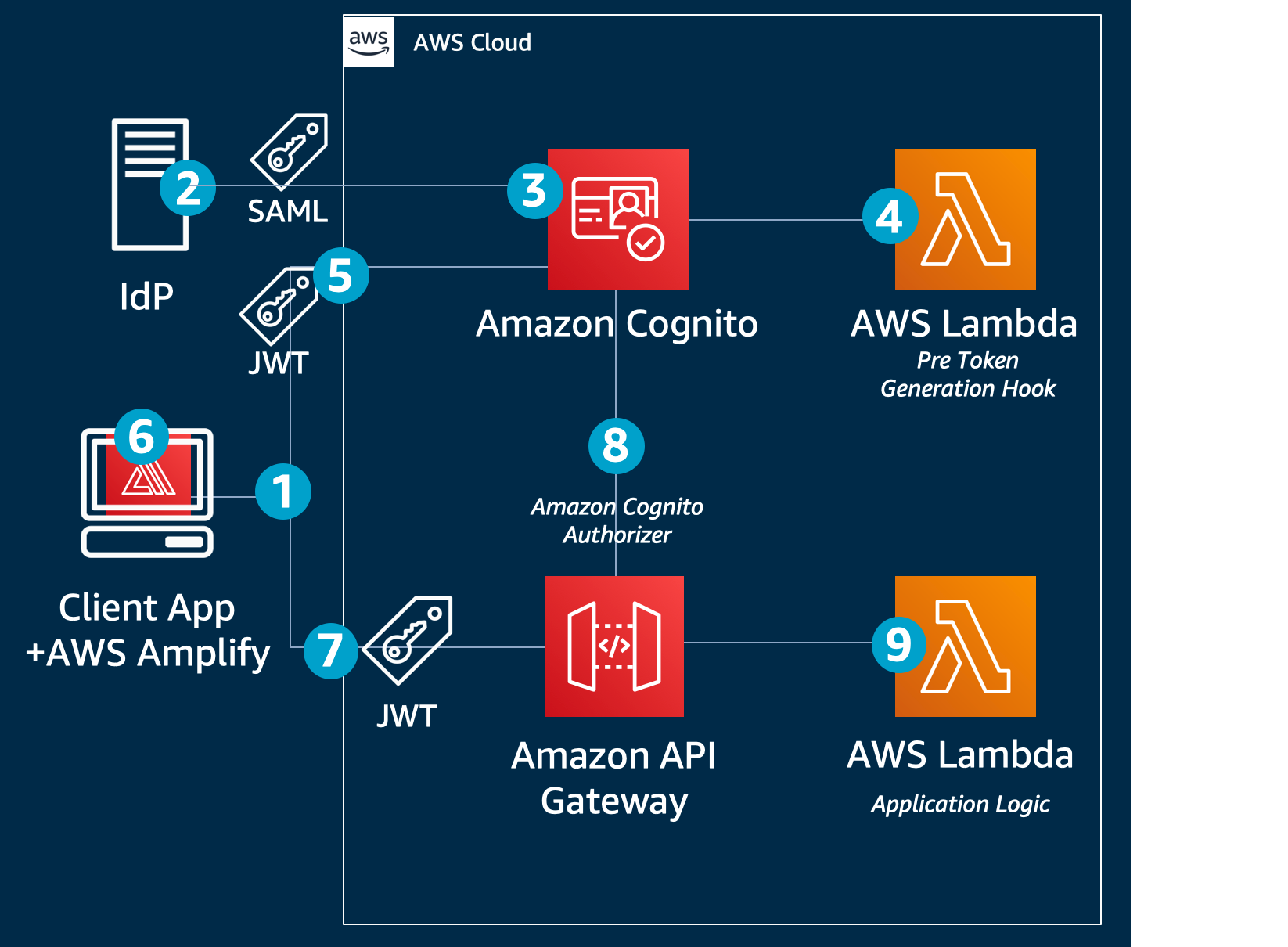
Role-based access control using Amazon Cognito and an external identity provider | AWS Security Blog

Integrate Amazon Redshift native IdP federation with Microsoft Azure AD and Power BI | AWS Big Data Blog

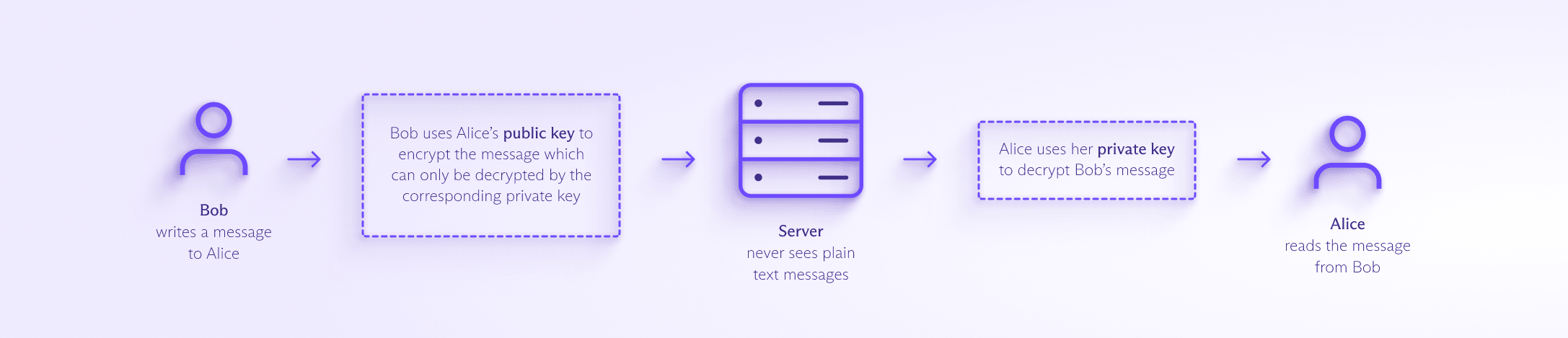
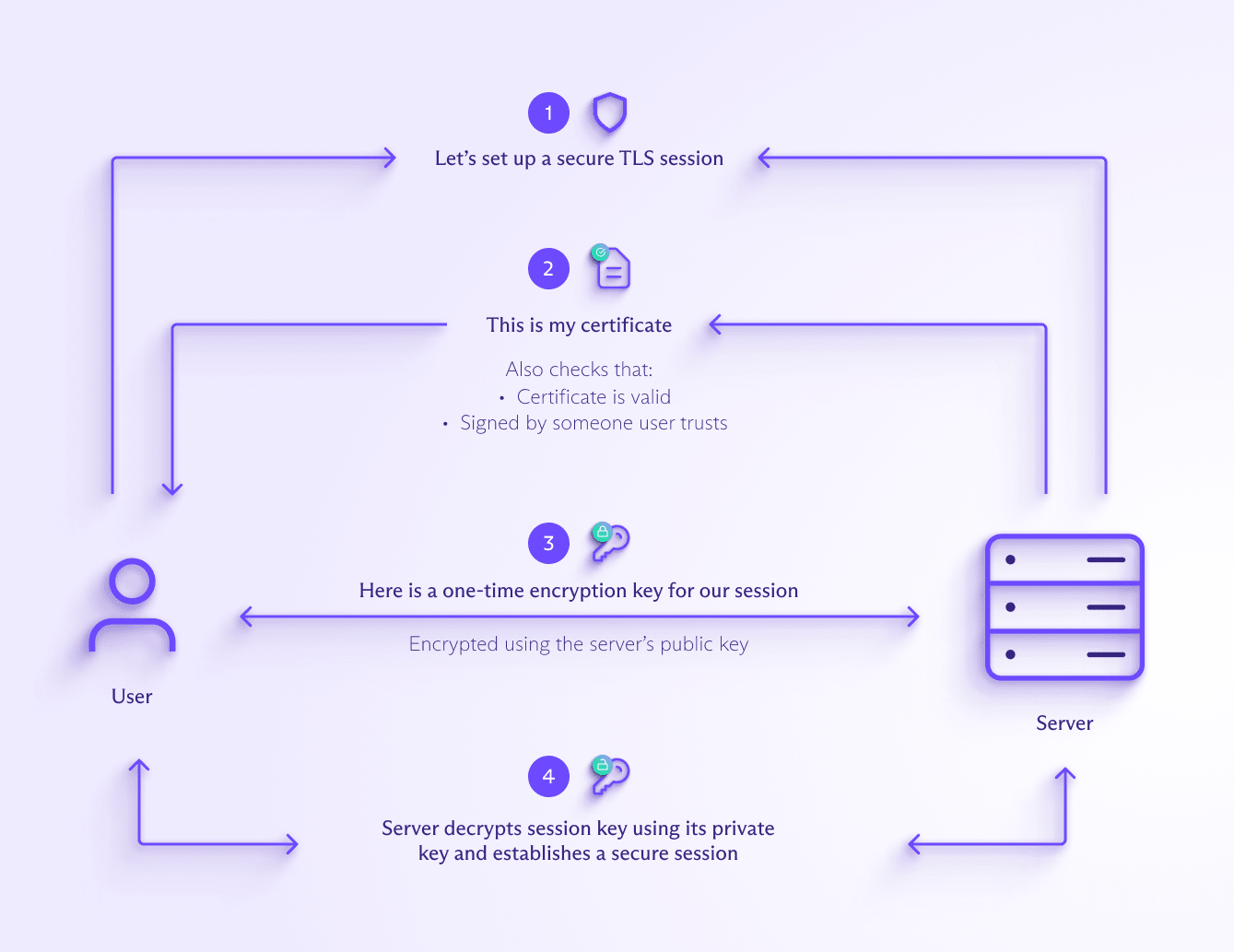
How encryption works in AWS: What assurances do you have that unauthorized users won't access your data? - FND310-R - AWS re:Inforce 2019 | PPT

How encryption works in AWS: What assurances do you have that unauthorized users won't access your data? - FND310-R - AWS re:Inforce 2019 | PPT